Elevate IT Security Principles
![]()
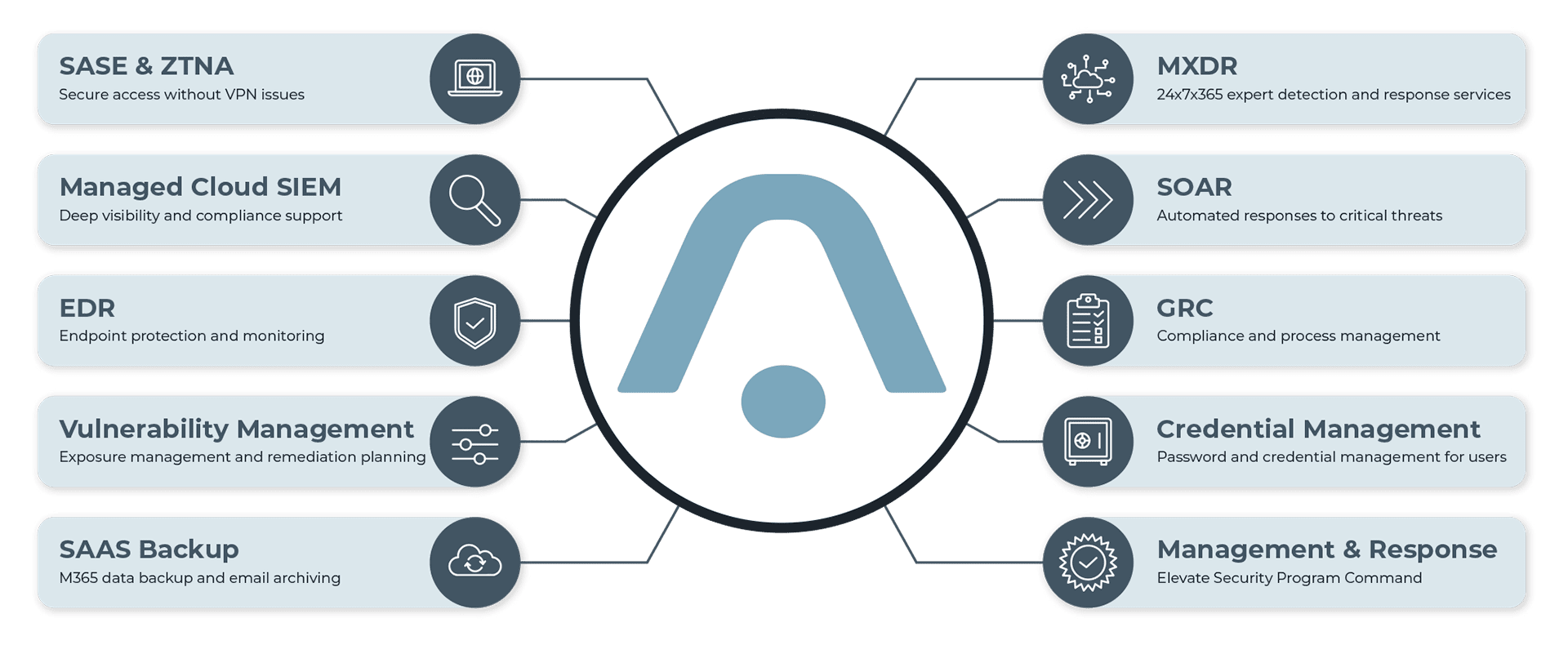
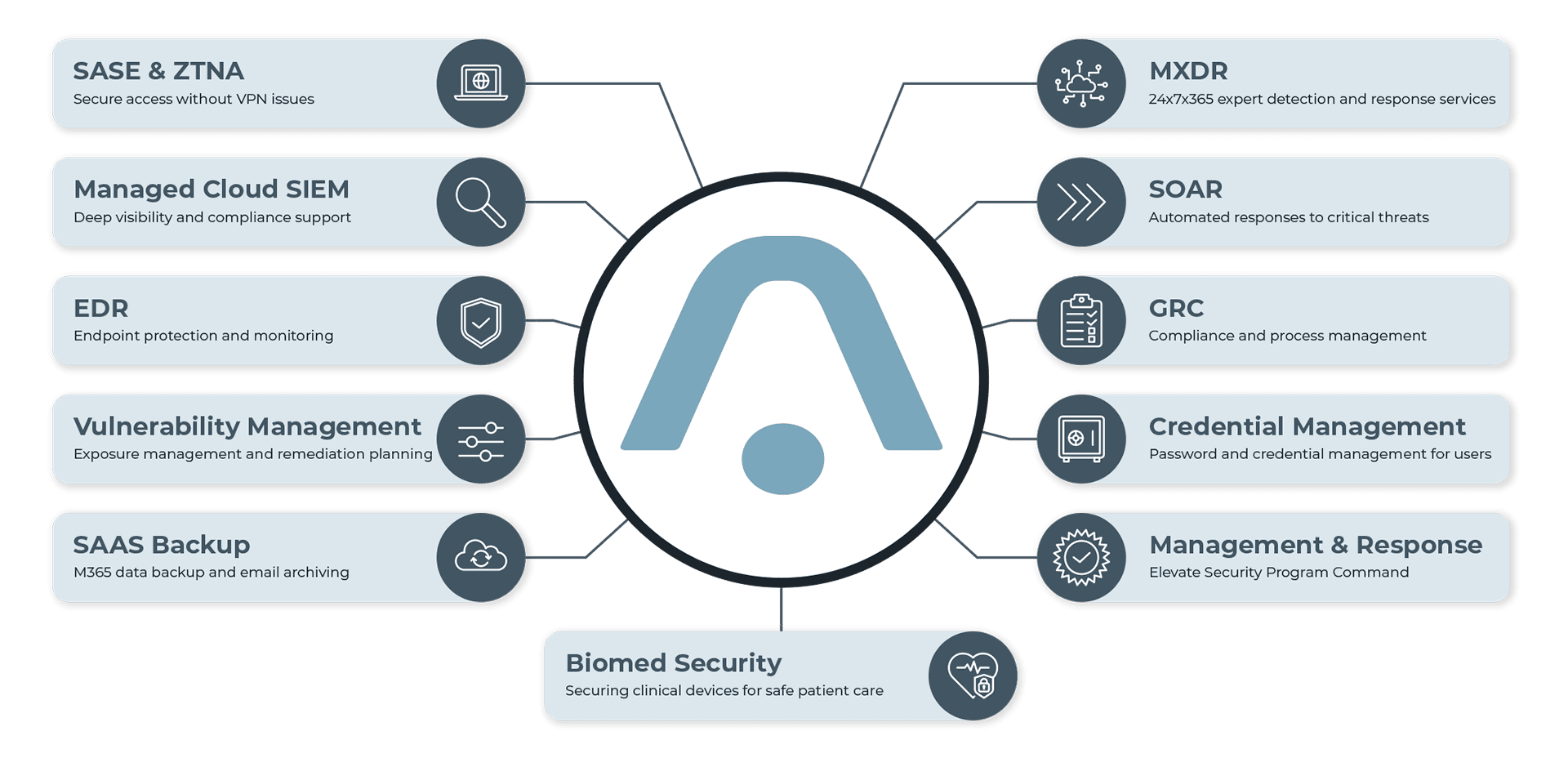
Protect
Remote work and cloud adoption have increased the need for tools that protect users, systems, and data beyond the traditional office. With modern security solutions and continuous monitoring, organizations can better safeguard access and reduce risk across distributed environments.
![]()
Detect
Even with the best protection tools, proactively watching for threats is a core tenet of great security. Having a 24x7x365 Security Operations Center (SOC) leveraging state of the art monitoring software (SIEM) will bring bad intentions into the light.
![]()
Inspect
In a constantly changing cloud world, the technology in use can become vulnerable overnight without good insight into where and why change occurred. Keeping an eye on changes with periodic vulnerability scans makes sure bad actors have no doors to enter.
![]()
Respond
The final step in great security is making sure tools and processes are in place to mitigate bad activities from causing severe harm and recovering from an attack expeditiously. With world class AI automation, (SOAR) routine incident response becomes more efficient and effective.
![]()
Recover
Even the strongest security programs cannot eliminate all risk. When a cyber incident becomes the priority, Elevate IT Security provides experienced leadership to guide response, contain threats, and restore operations quickly.
Why Organizations Need
The Elevate IT Security Platform
Security isn’t just a technical issue – it’s a business risk.
What The Data Shows
- Most breaches stem from basic failures – misconfigurations, unpatched systems, stolen credentials, or phishing, not a lack of tools.
- Human error and process gaps are the leading contributors to incidents.
- Organizations believe their controls are sufficient, yet still experience breaches due to poor execution or limited visibility.
The Reality Behind The Numbers
60–80% of incidents could be prevented or significantly reduced with proper use of existing controls, like patching, MFA, least privilege, monitoring, and backups.
But that doesn’t mean those controls were fully or correctly implemented. In many cases:
- Tools are misconfigured
- Alerts go unreviewed or unaddressed
- Controls aren’t fully deployed across the environment
- Processes, accountability, and training fall short
Where Things Break Down
- Endpoint detection tools generating alerts that no one monitors
- MFA is enabled in some areas, but not enforced everywhere
- Patch management systems are in place, but SLAs are not met
- SIEM and logging tools deployed without proper tuning or staffing
- Backups available, but never tested, leaving organizations vulnerable